The Escalation of Cyberwar through Language Manipulation
In the modern cyberwar landscape, information itself becomes a weapon. When states, extremist groups, or malicious actors don’t strike with code, they strike with words. The escalation doesn't begin with explosions—it starts with suggestions, distortions, and deceptions.
🟡 Middle-Phase Escalation: The Linguistic Battlefield
This is where misinformation and disinformation take center stage:
Term Meaning Intent
Misinformation False or misleading information shared unintentionally Often passive
Disinformation False information shared deliberately to deceive Active & hostile
Word Vending Crafting or selling manipulative phrases or headlines to twist a narrative or influence opinion Weaponized storytelling
Context Bending Taking something real, but reframing it to imply something false Subtle distortion
🧠 How They Interact in Cyberwarfare:
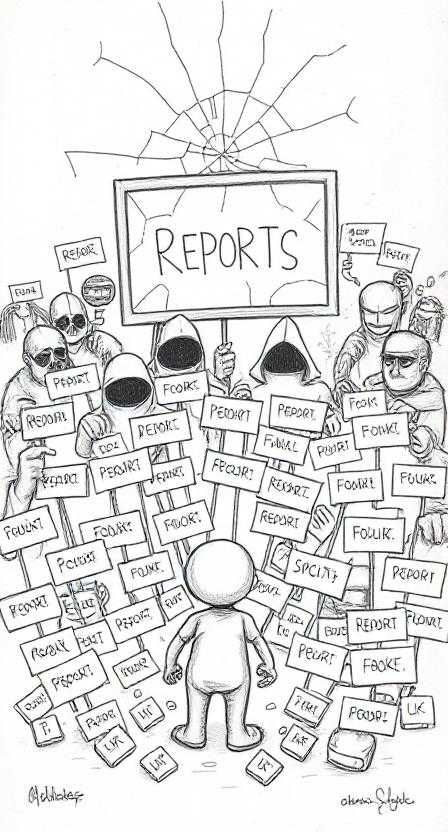
Disinformation seeds false claims (e.g., "This site is a phishing scam").
Bots/trolls amplify it across forums, reports, and social platforms.
Misinformed users believe and spread it without knowing it's fake.
Report systems are flooded, moderators overwhelmed, and real context lost.
Public trust erodes—in people, platforms, and truth itself.
📉 Impact on Society, Groups, and Individuals:
🔹 Society
Truth becomes subjective, vulnerable to viral manipulation.
People stop trusting institutions, experts, or even their peers.
Democracy and decision-making degrade—based not on fact, but echoed emotion.
🔹 Groups
Targeted groups (activists, startups, journalists) may face character assassination.
Polarization and infighting escalate due to false narratives.
Resource-draining distractions arise from defending against fake allegations.
🔹 Individuals
Lives can be destroyed by false reputations.
Creators self-censor to avoid controversy.
Legal, emotional, and social tolls become heavy.
⚠️ Red Flags That Signal Escalation:
Sudden rise in similar-sounding accusations.
Contradictory reports that seem emotional rather than factual.
Trending hashtags or keywords meant to mock, discredit, or defame.
Visuals (screenshots, videos) that are deceptively edited.
💬 Final Thought:
Modern cyberwar doesn’t always begin with firewalls—it begins with falsehoods. It is not only fought in the digital shadows, but also in the gray spaces between truth and lies.

Making fake reports—especially in the digital age—can be considered part of the early-to-mid escalation phase of cyberwarfare. It falls under psychological and information warfare, a tactic used to undermine trust, discredit individuals or systems, sow confusion, and provoke overreactions.
🔺 Escalation Phase Placement:
Early Escalation: When used to cause panic or confusion, such as fake reports of cyber attacks, crimes, or breaches.
Mid Escalation: When used systematically to target specific individuals, groups, or governments, intending to trigger legal actions, policy changes, censorship, or public backlash.
🔁 Impacts of Fake Reports:
🧑🤝🧑 On Individuals:
Reputation damage: False accusations can ruin careers or personal credibility.
Legal consequences: Victims may face wrongful investigations or even penalties.
Mental health impact: Stress, anxiety, and paranoia are common.
Self-censorship: Individuals may avoid expressing opinions or sharing content out of fear of being reported.
👥 On Groups/Organizations:
Trust erosion: Internal suspicion can rise, damaging team cohesion.
Disruption of operations: Time and resources are wasted responding to false allegations.
Manipulated perception: Public confidence in the group can drop, even without real wrongdoing.
🏙️ On Society:
Polarization: Falsified reports can deepen divisions and spread disinformation.
Distrust in institutions: People may lose faith in platforms, media, or governments perceived to act on false claims.
Weaponization of platforms: Reporting tools meant for safety get turned into tools of silencing or harassment.
⚠️ Signals of Weaponized Fake Reporting:
Sudden spike in reports targeting a specific group or ideology.
Identical language or patterns in multiple complaints.
Coordinated activity from botnets or troll farms.
Use of fake screenshots or deepfakes to support claims.
🛡️ Countermeasures:
Platform accountability: Require evidence-based review before acting on reports.
User education: Help users spot and resist manipulation.
Transparent appeals: Provide fair and timely mechanisms for those falsely reported.
Legal action: Criminalize intentional abuse of reporting systems when it leads to harm.
The Silent War: Unmasking the Modern Cyberwarfare Landscape
In today’s hyperconnected world, war no longer begins with tanks crossing borders or warplanes darkening the skies. Instead, it often starts in silence—through code injected into servers, unauthorized logins from remote corners of the globe, and subtle disruptions that cripple systems from within. This is the reality of modern cyberwarfare.
From Hacktivists to Terrorists: Weaponizing the Web
What began as underground activism—digital graffiti, website defacements, and data leaks—has evolved into something far more sinister. Terrorist organizations, once limited to physical battlegrounds, have found a new frontline: cyberspace. Here, the barriers to entry are low, the cost of attack is minimal, and attribution is often murky.
These groups have learned to weaponize cyber tools for propaganda, espionage, and destruction. Some examples:
Recruitment and Radicalization: They exploit social media algorithms to target and groom followers.
Funding Operations: Cryptocurrency and dark web markets allow for untraceable funding channels.
Cyber Sabotage: Attacks on critical infrastructure—like power grids, transportation systems, and hospitals—are used to cause chaos and incite fear.
What makes cyberwarfare especially dangerous in the hands of terrorists is the lack of rules. Unlike nation-states, terrorist actors are not bound by international law or ethics, making them more unpredictable and more aggressive in their tactics.
Levels of Cyberwar Escalation (Based on Interest and Impact)
Level 0 – Reconnaissance & Surveillance
Interest: Intelligence gathering
Social engineering attacks, phishing campaigns, and scanning for vulnerabilities.
Indications: Increase in unusual login attempts, traffic from suspicious IPs, and targeted spear-phishing.
Level 1 – Psychological Operations & Propaganda
Interest: Ideological influence and recruitment
Use of fake news, manipulated media, and fearmongering content to polarize and destabilize societies.
Indications: Surge in disinformation campaigns, coordinated bot activity, and algorithm manipulation.
Level 2 – Data Breaches & Theft
Interest: Sabotage or financial gain
Extraction of sensitive data, defacing websites, or exposing private communications.
Indications: Leaked databases appearing on dark web, ransom demands, or fake accounts targeting key personnel.
Level 3 – Infrastructure Disruption
Interest: Strategic and tactical advantage
Attacks on power grids, water systems, telecom networks, and financial systems.
Indications: Rolling blackouts, service outages, or unexplained system failures affecting large regions.
Level 4 – Full-Scale Cyberwarfare
Interest: Long-term destabilization, warfare substitute
Coordinated attacks across multiple sectors (military, health, finance) often during political unrest or military conflict.
Indications: National emergency declarations, mass-scale system lockdowns, government warnings, or cyber retaliation between states.
Signs That a Cyberwar May Already Be Happening
Frequent "zero-day" exploit attacks with no known patches.
State-level blame games, such as official statements accusing other countries or factions of cyberattacks.
Sudden shutdowns of infrastructure that are blamed on “technical errors” with vague details.
Increase in data leaks, especially of government or military systems.
Tighter internet censorship, surveillance, or control measures introduced rapidly.
A shift in media language, using terms like "digital battlefield," “cyber retaliation,” or “state-sponsored intrusion.”
Conclusion: A War Without Borders
Modern cyberwar isn’t about who has more missiles—it's about who controls information, who owns the digital terrain, and who can strike unseen. As terrorists and state-backed groups become more skilled and better equipped, the line between peace and war becomes increasingly blurred.
We may not hear the sirens or see the smoke, but if you listen closely—through the breach reports, the dark web chatter, the DNS outages, and the sudden silence of once-vibrant platforms—you'll realize: the cyberwar may have already begun.

WS WOE
In today's world, where cybersecurity threats loom larger than ever, ethical hacking has evolved into one of the most critical fields in technology. Ethical hackers, also known as "white hats," are cybersecurity professionals who use their skills to protect systems rather than exploit them. However, diving into ethical hacking without a solid foundation can be like building a house on sand — unstable and risky.
Understanding Before Acting
Ethical hacking is not just about knowing how to break into systems; it's about understanding why systems are vulnerable, how to secure them, and what the consequences of security flaws can be. Without a deep understanding of networking, operating systems, coding, and cybersecurity principles, an aspiring ethical hacker might miss crucial details or, worse, accidentally cause harm. A solid foundation ensures that ethical hackers can think critically, act responsibly, and truly protect the digital world.
A Must-Have for Serious Professionals
Taking ethical hacking classes without prior knowledge in IT basics is like learning to perform surgery without studying human anatomy. Topics like TCP/IP protocols, encryption methods, firewalls, and system architecture are prerequisites to becoming a competent ethical hacker. Otherwise, it’s easy to get overwhelmed or, even worse, develop bad habits that could later be costly in real-world scenarios.
Ethics First, Skills Second
One of the core principles of ethical hacking is responsibility. Understanding the legal and ethical boundaries is non-negotiable. A person who masters the technical skills without a strong ethical mindset can easily cross into "black hat" territory. That's why solid training should always emphasize not just the 'how' but also the 'why' and 'when' of ethical hacking practices.
Invest in a Proper Learning Path
For anyone planning to enroll in ethical hacking courses or aiming to work in the field, it's crucial to:
Start with fundamentals: Networking, programming (Python, C/C++), Linux, and cybersecurity basics.
Build ethical awareness: Study the laws, best practices, and industry standards.
Gain practical experience: Set up home labs, use penetration testing frameworks legally, and always practice in controlled environments.
Conclusion
Ethical hacking is an exciting and rewarding career, but it demands respect, discipline, and a rock-solid understanding of the underlying technologies. Rushing into it without preparation can lead to frustration, mistakes, or worse, unintentional harm. Build your foundation strong, embrace continuous learning, and always uphold the ethics that the role demands. Only then can you truly call yourself a guardian of the digital world.
Ready to start your journey? Begin by strengthening your fundamentals. Remember, real cybersecurity heroes are not just skilled — they're also wise

Top 10 Controversial Cybercrime Cases in the Philippines
1. "ILOVEYOU" Virus (2000)
Key RTC: None (no cybercrime law yet).
Judge: None.
Defense: Virus was not illegal at the time.
Attorney: Onel de Guzman's lawyer (unnamed).
Outcome: Walked free.
Reference: BBC News - 'Love Bug' creator tracked down
2. COMELEC Data Breach ("Comeleak", 2016)
Key RTC: DOJ investigation only.
Judge: None.
Defense: It was "just" website defacement.
Attorney: COMELEC internal lawyers.
Outcome: Chairman Bautista found negligent by the National Privacy Commission.
Reference: Rappler - NPC holds Comelec liable for data breach
3. Ang Totoong Narco List - "Bikoy" Videos (2019)
Key RTC: Makati RTC Branch 138.
Judge: Judge Andres Soriano.
Defense: Bikoy claimed he was manipulated by political figures.
Attorney: Briefly represented by Atty. Larry Gadon.
Outcome: Cases pending; countersuits filed.
Reference: CNN Philippines - 'Bikoy' surrenders to police
4. #PulisPatola Cyberlibel Threats (2021)
Key RTC: No formal cases filed.
Judge: Not applicable.
Defense: Free speech rights.
Attorney: Netizens supported by FLAG (Free Legal Assistance Group).
Outcome: No major convictions.
Reference: Inquirer - PNP Cybercrime Group to file cyber libel cases
5. Arrest of Maria Ressa (2020)
Key RTC: Manila RTC Branch 46.
Judge: Judge Rainelda Estacio-Montesa.
Defense: Cybercrime law should not be retroactive.
Attorney: Atty. Theodore Te (former SC spokesperson).
Outcome: Convicted of cyberlibel, pending appeal.
Reference: Rappler - Maria Ressa convicted of cyberlibel
6. EdTech Platform Hacking (2021)
Key RTC: None formalized; mostly handled internally by schools.
Judge: Not applicable.
Defense: Students cited system vulnerabilities.
Attorney: Unknown/Private defense.
Outcome: Disciplinary action only.
Reference: Manila Bulletin - Students hack LMS during online classes
7. BDO and UnionBank Cyberheist (2021)
Key RTC: Civil suits filed in Makati and Taguig.
Judge: Pending.
Defense: 3rd-party compromise.
Attorney: BDO internal legal + Sycip Salazar law firm.
Outcome: Partial refunds; criminal investigation ongoing.
Reference: ABS-CBN - BSP says BDO, UnionBank responsible for unauthorized transactions
8. Miss Universe Philippines Vote-Rigging Allegations (2020)
Key RTC: No case filed.
Judge: None.
Defense: Voting system was "secure."
Attorney: No case, no formal lawyers engaged.
Outcome: Public criticism only.
Reference: Philstar - Miss Universe Philippines explains voting controversy
9. Celebrity Deepfakes Scandal (2022)
Key RTC: No filed case yet.
Judge: None.
Defense: No defense presented (anonymous hackers).
Attorney: Celebrities advised by big firms (Divina Law, ACCRA Law).
Outcome: Senate hearings on AI and deepfakes initiated.
Reference: Inquirer - Deepfake scandals threaten celebrities
10. SIM Card Registration Phishing Surge (2023)
Key RTC: Under NBI Cybercrime Division probe.
Judge: None yet.
Defense: Telcos claimed third-party phishing.
Attorney: Telcos using internal legal teams.
Outcome: Cases under investigation, Senate proposing amendments.
Reference: GMA News - SIM card registration scams on the rise

